Goodwill Industries of New Mexico is working with a team of forensic experts to "understand the extent and implications of" what appears to be a cybersecurity incident involving its network.
Albuquerque Business First contacted the Albuquerque-based nonprofit organization on Tuesday after the publication found that users of LockBit 3.0 claimed to have nearly 250 gigabytes of data from “goodwillnm.org.” That URL matches Goodwill Industries of New Mexico’s website, and the claim included the organization's logo and a description that matches the text on the “About Us” section of its website.
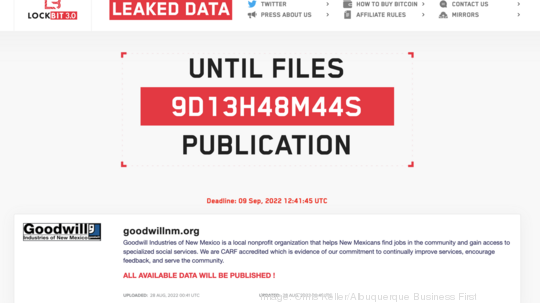
The ransomware claim shows it was posted sometime on Sunday. It contains screenshots of file directories containing the organization's data and gives a deadline of the morning of Sept. 9 before the site will publish the available data.
In a statement provided to Business First, Goodwill Industries of New Mexico said it recently discovered the incident which impacted its network environment.
"While these types of situations have become all-too-common nationwide, we recognize the significance of this event and have quickly taken the appropriate steps to address it. Our comprehensive assessment is ongoing and may span several weeks. Part of the assessment will include an analysis of whether personal information related to employees, customers, donors, and vendors are involved. If we determine that personal information was involved in the incident, we will notify those individuals in accordance with applicable law. Rest assured that we are committed to sharing more information as soon as it becomes available," the statement continued.
The ransomware claim was posted on the LockBit 3.0 site, which is accessible through Tor hidden services. Tor hidden services are essentially websites that can only be accessed using specific web browsers. Ransomware gangs and other malicious actors post their actions to these sites.
In the cybersecurity world, LockBit 3.0 is the latest version of a particular flavor of ransomware. It succeeds LockBit 2.0, which was the subject of an FBI alert in early February that detailed various “indicators of compromise” — essentially evidence or markers — associated with this particular flavor of ransomware.
“The FBI is seeking any information that can be shared, to include boundary logs showing communication to and from foreign IP addresses, a sample ransom note, communications with the threat actors, Bitcoin wallet information, the decryptor file and/or a benign sample of an encrypted file,” the FBI alert stated.
The LockBit flavors are billed as “Ransomware-as-a-Service.” Essentially, it’s developed by a group that offers to would-be “affiliates” — hackers and malicious actors who use the ransomware and boast of their exploits in the same way a software provider would highlight its clients.
Allan Liska, who works for the Massachusetts cybersecurity firm Recorded Future as an intelligence analyst and member of its computer security incident response team, said the 3.0 version of LockBit ransomware is essentially new software, which meant the group created a new backend system and a new site to post its claims.
“Ransomware groups are like any other software developers, constantly making improvements to their software,” Liska told Business First via an encrypted message.